Active Directory Logs Event Viewer
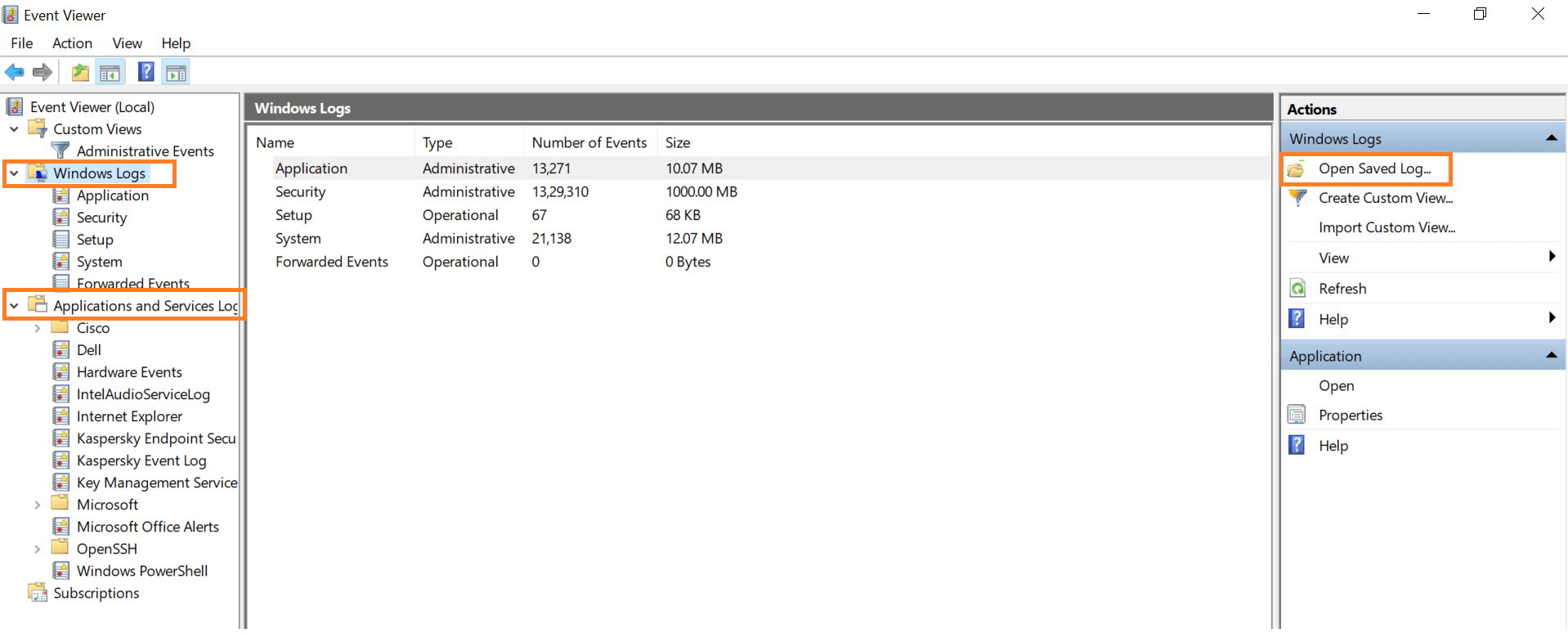
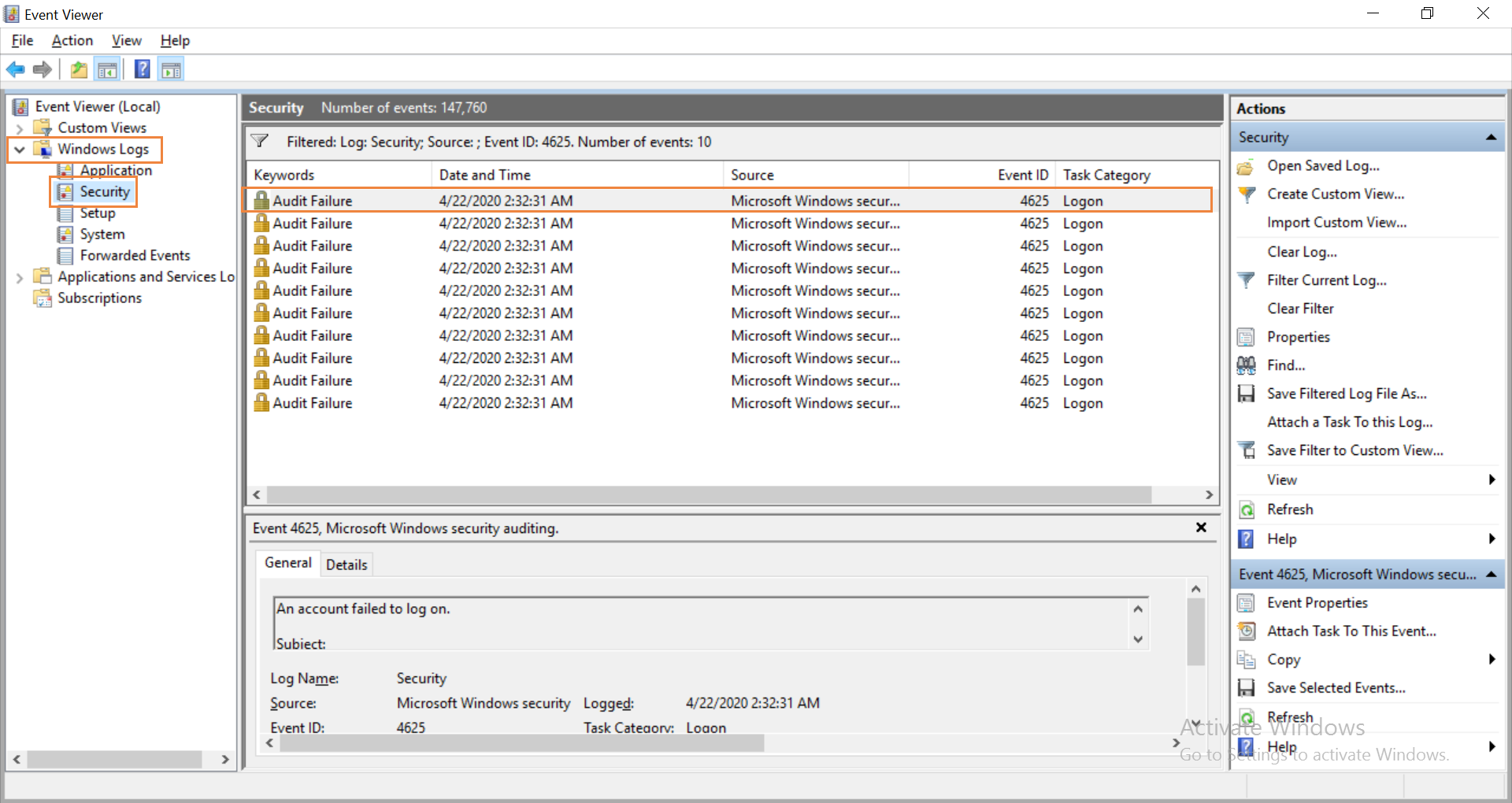
4726 (user account deletion) and 4743 (computer account deletion). In the event viewer, navigate to windows logs and select security.
How To Audit Who Logged Into A Computer And When
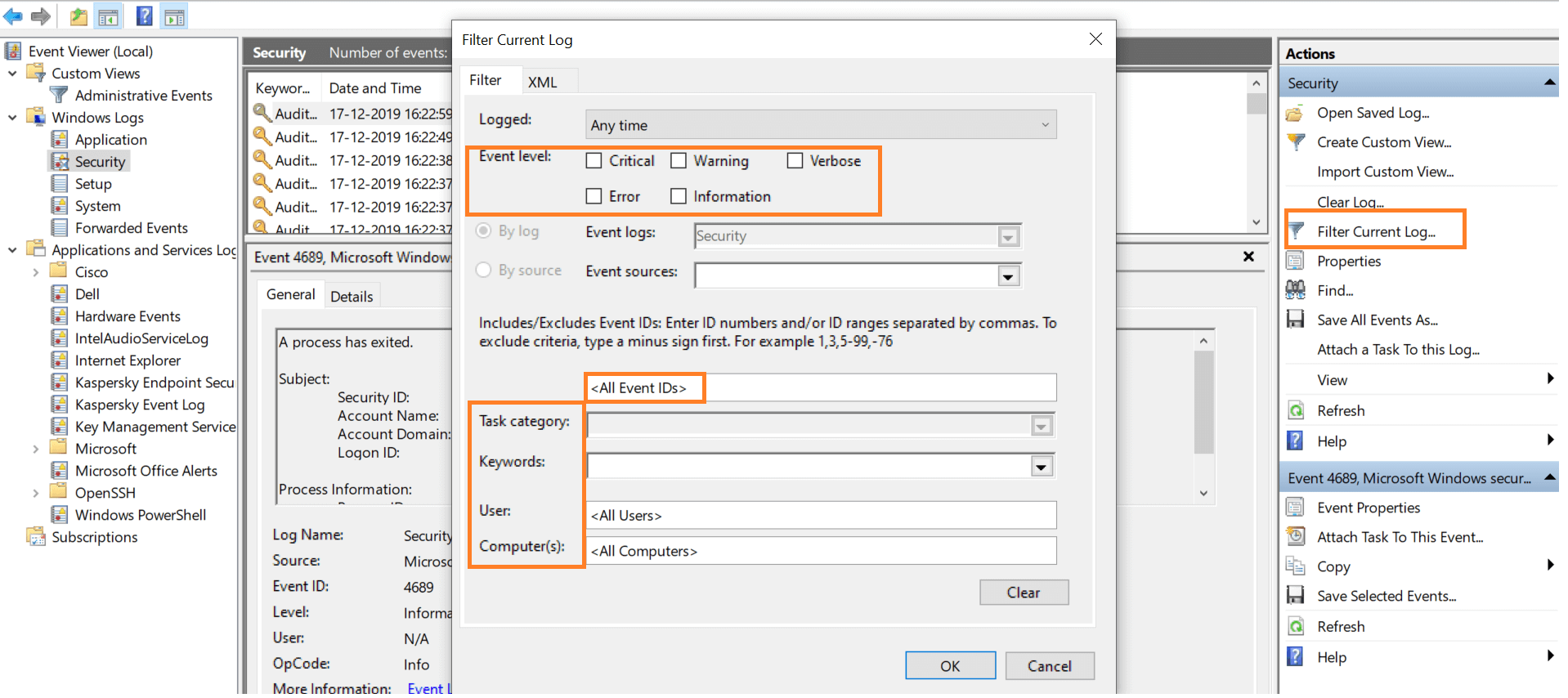
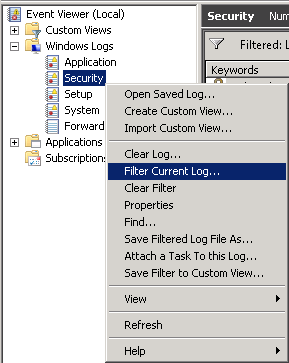
Then, simply click filter current log.
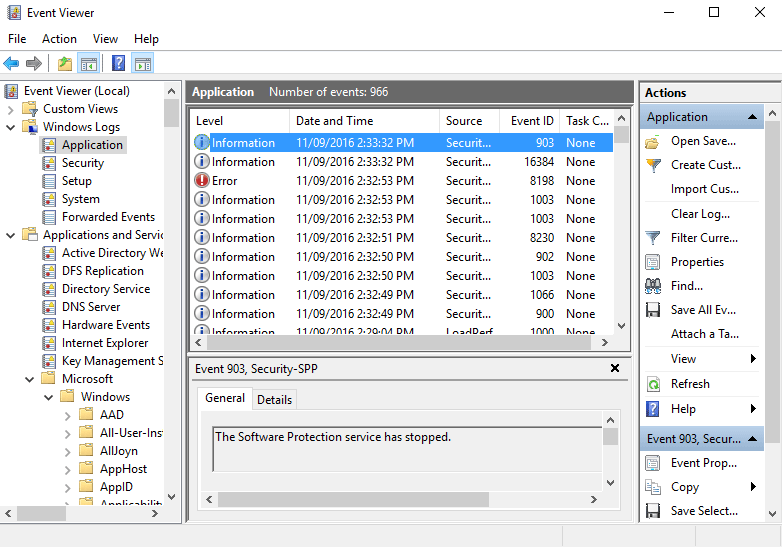
Active directory logs event viewer. Open “event viewer”, and go to “windows logs” “security”. You can also detect possible security threats with reports on anomalous logon activity and automate responses to such threats. A solid event log monitoring system is a crucial part of any secure active directory design.
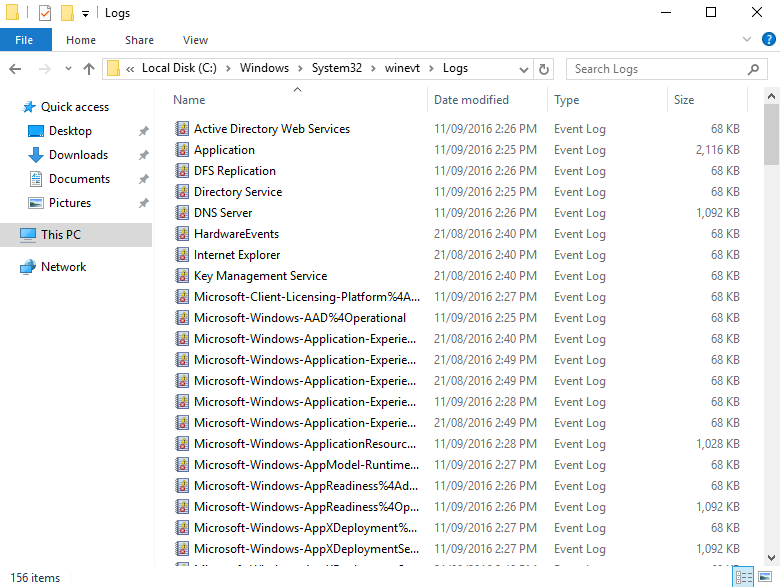
A small, nearly hidden feature of the event viewer by microsoft is the ability to autoarchive the logs. Save as a csv (comma separated value) file. After you enable active directory auditing, windows server writes events to the security log on the domain controller.
Search for event id 4724 in security logs. In above image event id 4720 refers to ‘user account creation’. This event id identifies account’s password changes attempted by an administrator.
Event viewer is the native solution for reviewing security logs. It is free and included in the administrative tools package of every microsoft windows system. It is free and included in the administrative tools package of every microsoft windows system.
Go to “windows logs” “security”. Many computer security compromises could be discovered early in the event if the victims enacted appropriate event log monitoring and alerting. Search for the event id:
Active roles continues to function but the license agreement is violated. For example, the 2009 verizon data breach report states: To grant access to event logs of your dcs, simply add your user as a member of event log readers domain group.
Track logon session using event logs. You can also search for these event ids. Go to event viewer → filter directory service logs to locate the event id 2887 (windows server 2003 to 2012) number of ldap queries go to event viewer → filter directory service logs to locate the event id 1643 (windows server 2003 to 2012)
After the license has expired, the directory management function of active roles is. The local group should grant access to event logs of a specific member server. Open “filter current log” on the rightmost pane and set filters for the following event ids.
We can review events using server manager too. Perform the following steps in the event viewer to track session time: Event viewer is the native solution for reviewing security logs.
Most common way is to review events under event viewer mmc. Enter a file name that includes the log type and the server it was exported from. The active roles license will expire in {2} days.
The current number of enabled user accounts in ad ({0}) exceeds the licensed number ({1}). The logs of active directory is stored in the event viewer of windows os. In the “filter current log” window, simply enter the particular event id and carry out the search operation.
Archive all the logs from windows in a zip file. These event ids identify the user and computer account deletions. Once auditing is enabled, perform the following steps in event viewer to view the events:
Of course, one of the most important event viewer logs is the security log. Active directory | march 20, 2015 | 2 min read. Filtering the security event log;
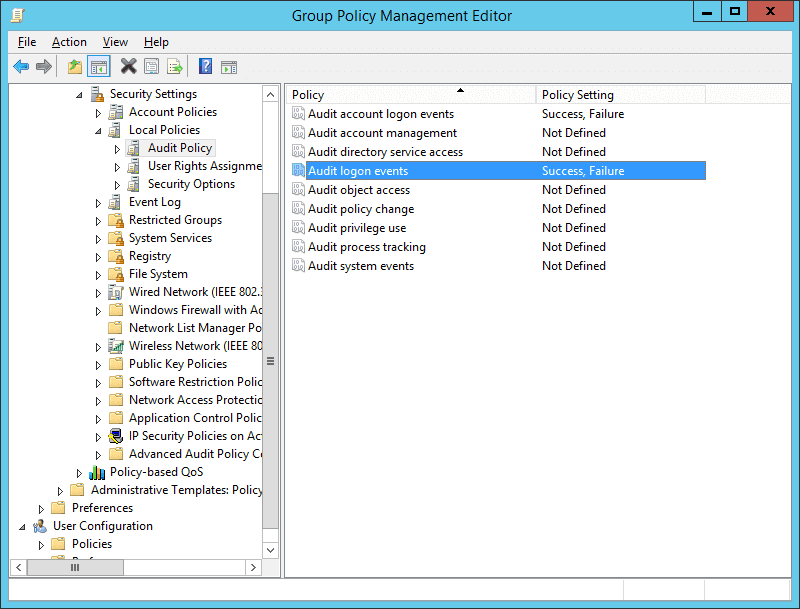
Last updated on november 8, 2017 by dishan m. Perform the following steps to view the events: In order to see these event ids in event viewer (either logged in directly to your domain controller or remotely) you'll need to create a group policy object for your domain controller(s):
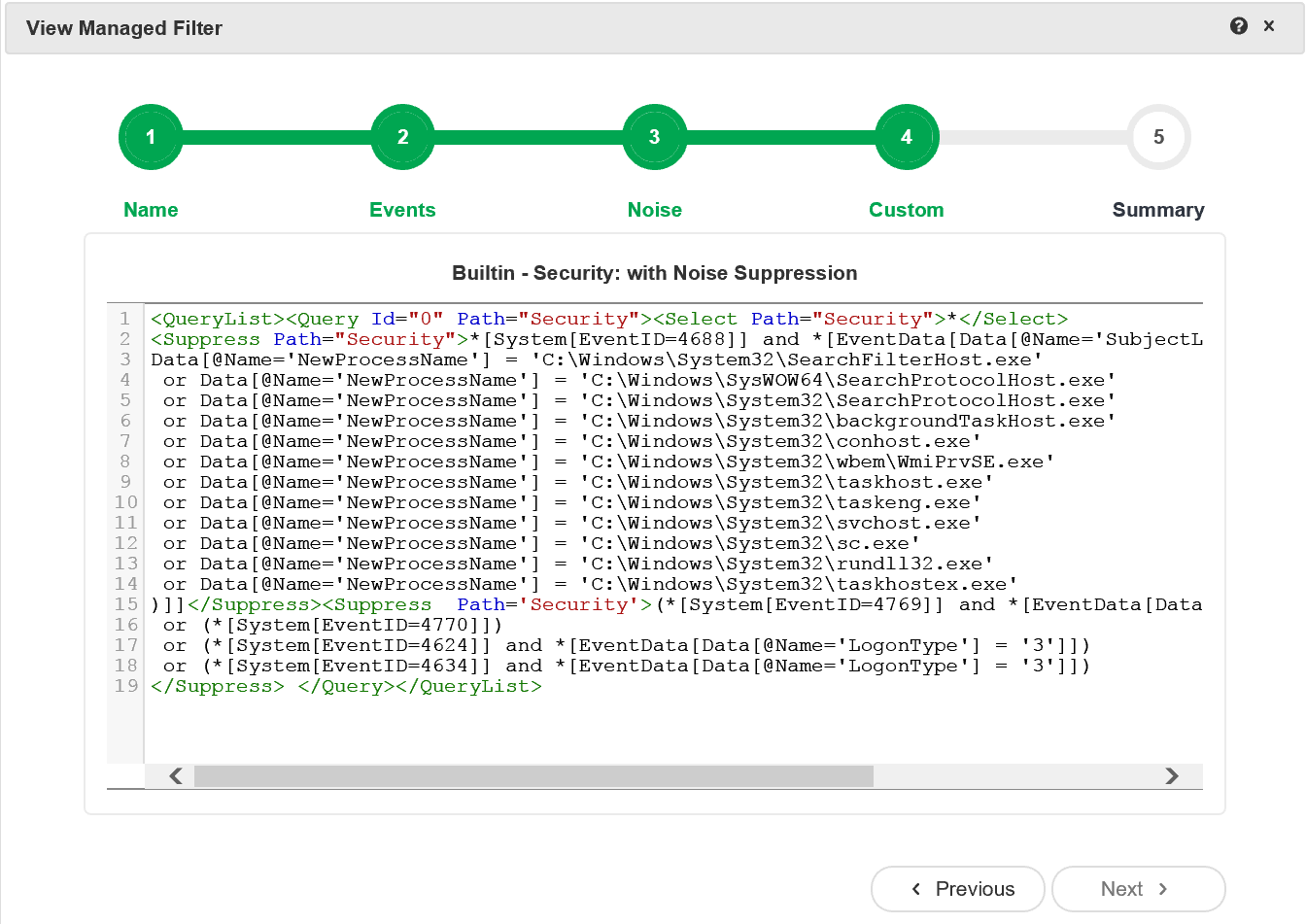
Since most of the readers will be familiar with the event viewer, this section only mentions a few things as they relate to active directory troubleshooting. Securing active directory first and foremost, you need to configure your audit policy so that windows can record the relevant events in the security log. To enable ldap debugging logs on the domain controller, set the ldap interface events to verbose using dword value 5 in the windows registry.once ldap events have been enabled, open the windows event viewer and.
Open “event viewer” console and go to “windows logs” “security”. Can anyone please help me why its showing empty or its default nature of windows 2012 r2. If you are using the server manager, navigate to.
Then logs generating in event viewer but logs not generating. Locate the log to be exported. Next, you need to aggregate and analyze the collected logs, then translate those findings into actionable information, like reports and alerts.
If you would like to grant access to some member servers then you can use restricted groups gpo to do that or do it manually: Independent reports have long supported this conclusion. There are different ways to review active directory service related logs in a domain controller.
View logs in event viewer. I have promoted windows 2012 r2 adc. After you enable active directory auditing, windows server writes events to the security log on the domain controller.
Active directory related event ids the windows server 2000 and 2003 event ids for directory service Open event viewer (run → eventvwr.msc). The event viewer in windows server 2008 can be accessed via the computer manager or the server manager, by running eventvwr.msc, or by starting it directly from administrative tools.
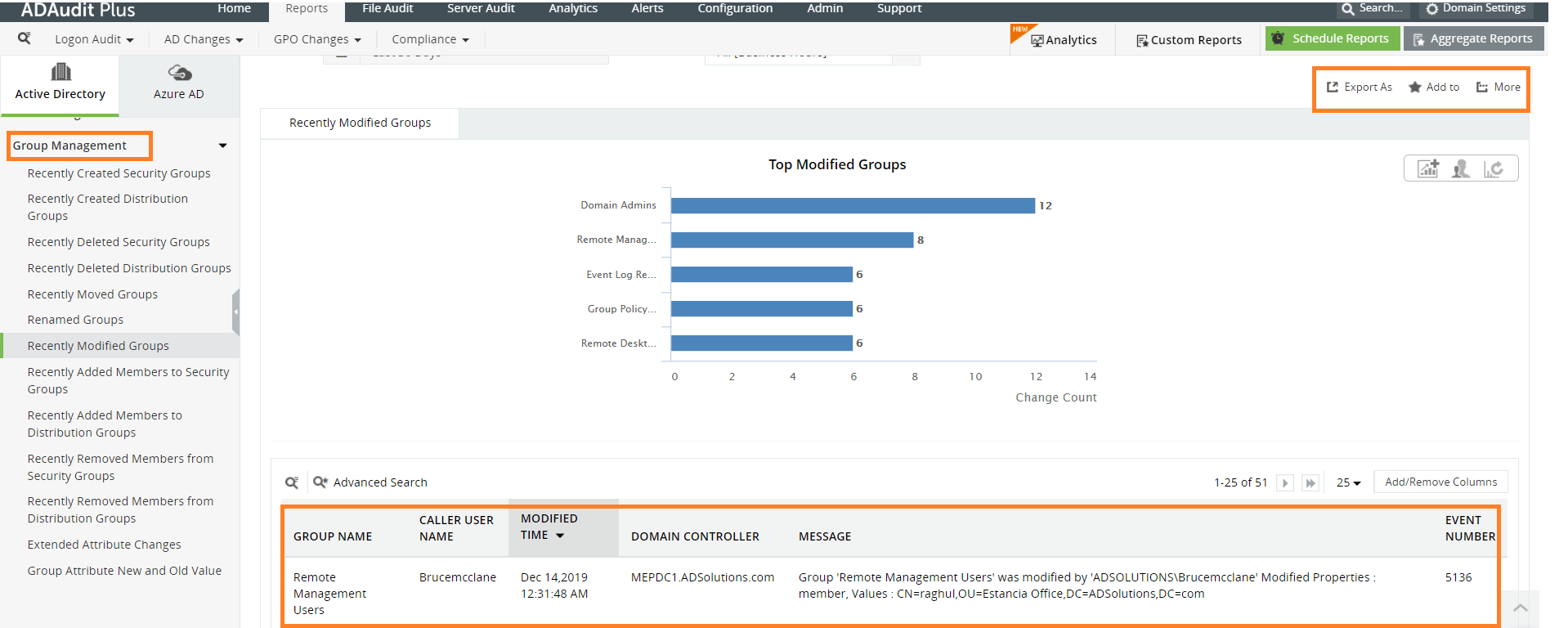
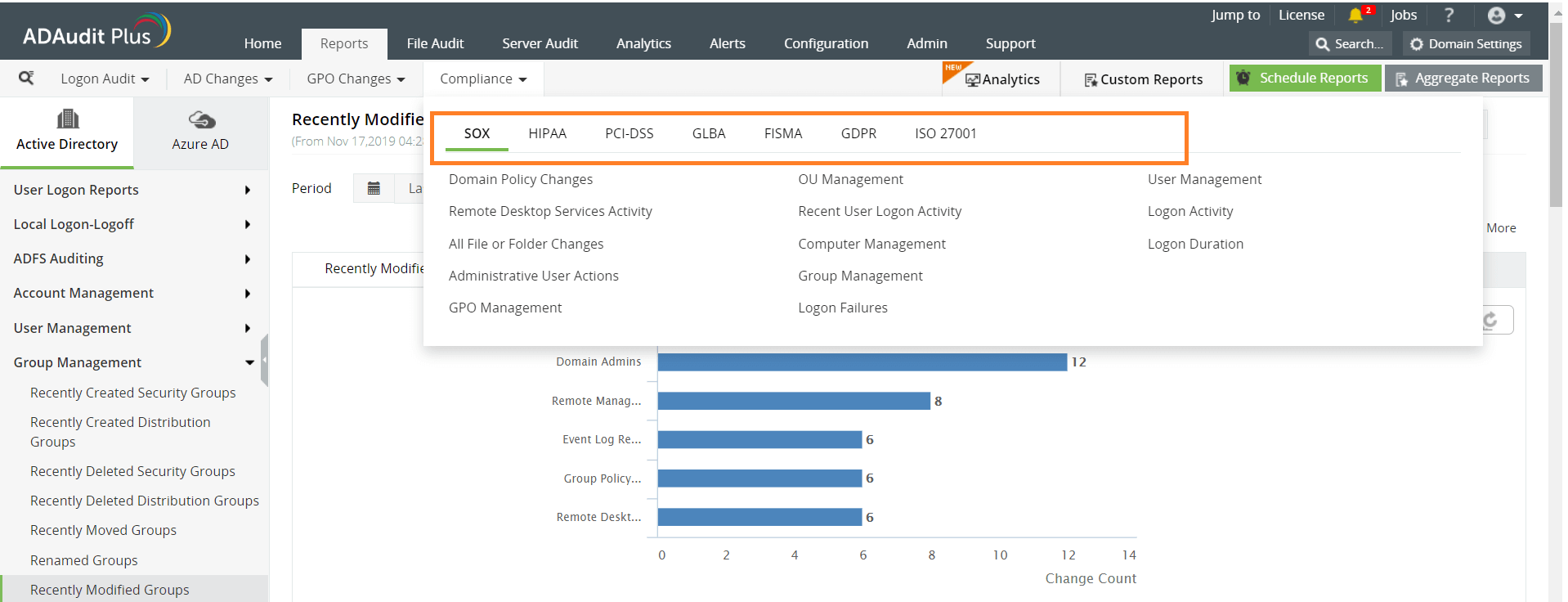
I'll list the event ids you're concerned with: Examining ldap interface events in the windows directory service event log can help determine if a bad password or bad username is the cause of the authentication failure. Manageengine adaudit plus is an active directory auditing tool that can help monitor user logon activity using kerberos authentication events.

Adjusting Event Log Size And Retention Settings
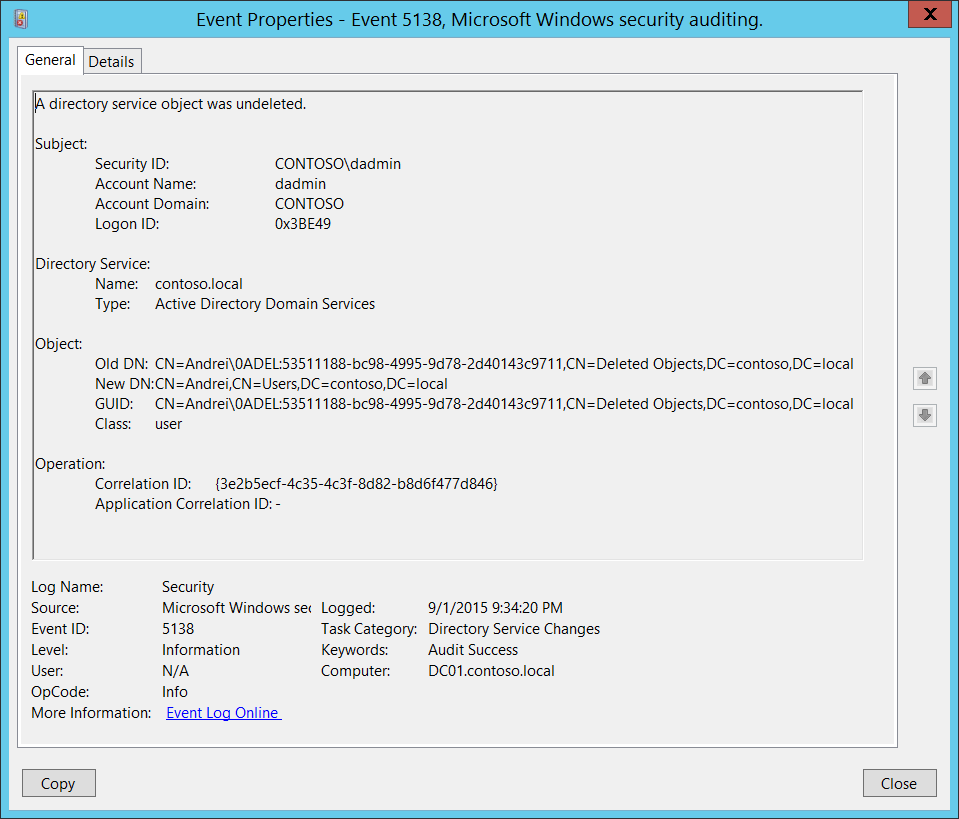
5138s A Directory Service Object Was Undeleted Windows 10 - Windows Security Microsoft Docs
Identify Source Of Active Directory Account Lockouts Troubleshooting
Windows Security Log Event Id 4740 - A User Account Was Locked Out
Where Are Windows Server 2016 Log Files Stored
.jpeg)
Dns Logging And Diagnostics Microsoft Docs

Adjusting Event Log Size And Retention Settings
How To Find The Source Of Failed Login Attempts Manageengine Adaudit Plus
How To Check Event Logs In Windows Server 2012
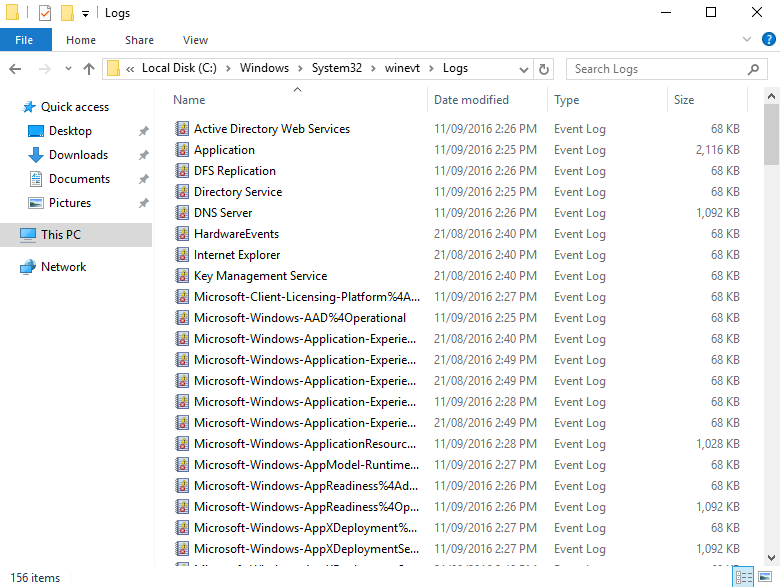
Where Are Windows Server 2016 Log Files Stored

Remote Event Log Viewing - Windows Forum
Tracking And Analyzing Remote Desktop Activity Logs In Windows Windows Os Hub